Merge two codebases: pick one source of truth and migrate cleanly
Merge two codebases without duplicating bugs by picking a clear source of truth, migrating features step by step, and validating auth, data, and security.
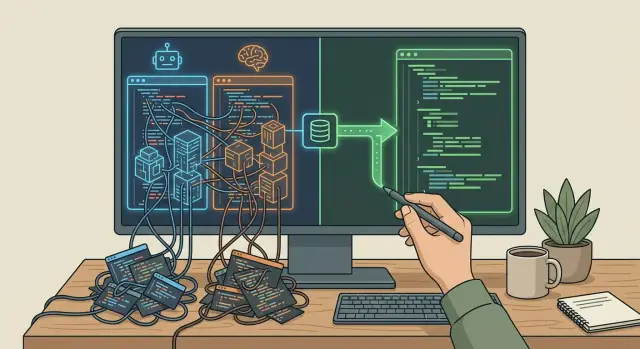
Why two AI-built codebases become a problem fast
Two AI tools can produce two very different versions of the same app in a weekend. Maybe you started in v0 for speed, then rebuilt in Replit when things got messy. Or a teammate tried Lovable or Bolt and "fixed" a few screens there. Each repo can look believable on its own, so it’s tempting to keep both and sort it out later.
That’s where the trouble starts. Prototypes diverge quickly. The UI might look similar, but the logic underneath often isn’t. One repo stores roles in a table, the other keeps them in a JSON blob. One assumes email login, the other assumes OAuth. A week later you don’t just have two codebases. You have two sets of assumptions.
Common failure modes show up fast:
- The same bug exists twice, but with different symptoms.
- Business rules conflict (pricing, permissions, status rules), so “correct” depends on which repo you run.
- Data models drift, making migrations risky and reporting unreliable.
- Security fixes land in only one place, leaving the other as a trap.
Trying to merge two codebases line-by-line usually makes things worse. You end up stitching together mismatched patterns, copying broken auth flows, and pulling in unsafe queries or leaked secrets from the weaker repo. The result is a third codebase that’s harder to understand than either original.
A good outcome is simple: one source of truth codebase, one deployment path, and one place to fix bugs. You can still reuse good ideas from the other repo, but only by migrating features intentionally. The goal isn’t “combine everything.” It’s “choose one to trust, then move only what you can verify.”
What “source of truth” means (and what it doesn’t)
A source of truth codebase is the one place where new changes are allowed to land. If a feature ships, it ships from there. If a bug is fixed, the fix goes there. Everything else becomes reference material, not a second live product.
It doesn’t mean the chosen repo is perfect, clean, or even the one you like best. It also doesn’t mean you delete the other repo on day one. You can keep it for comparisons or use it to understand what users expect. The difference is governance: only one repo moves forward.
Before you pick, define what “truth” covers so you don’t fight about it later. Keep it plain:
- Product behavior (features and key UX flows)
- Data model and migrations
- Authentication and permissions
- Deployment setup and environment configuration
- Logging and error handling
Then set one rule everyone follows: the winning repo is the only writable path. The other becomes read-only and stays that way.
Also set a decision deadline. AI-generated prototypes drift fast, especially when two tools keep generating new files. A practical target is 24 to 72 hours: pick one, freeze the other, then migrate intentionally. If you’re unsure which repo is safer, a quick audit can surface high-risk problems early, especially around auth, secrets, and database writes.
A quick way to compare two codebases without deep expertise
When you need to merge two codebases, don’t start by debating which one “looks nicer.” Start by checking which one behaves like real software under basic pressure: run, build, deploy, and fail in predictable ways.
A simple scorecard forces a fair comparison. Give each repo a 0-2 score (0 = fails, 1 = shaky, 2 = solid) for:
- Runs locally from a clean install (no secret manual steps)
- Builds and deploys in a repeatable way
- Has at least a few meaningful tests (or you can add them quickly)
- Avoids hacks (hard-coded URLs, copied config, random workarounds)
- Produces clear errors you can act on (not silent failures)
Next, scan for red flags you can spot without being a security specialist: secrets committed to the repo, “temporary” auth bypasses, raw SQL built from user input, or API routes with no access checks. If one repo has obviously broken auth or clear injection risks, assume it’s a deeper problem than it looks.
Then look at structure and build hygiene. A healthier repo usually has an obvious layout (UI, backend, migrations), environment variables in one place, and one clear way to run and deploy. If logic is duplicated across random files, naming is inconsistent, or there are multiple competing config files, you’ll pay for it later.
Finally, run a simple maintainability test: can a new person find where login happens, where data is stored, and where the main API routes live in 30 minutes? If not, bugs will keep coming back after “fixes.”
Step-by-step: choose the winning repo and freeze the other
Keeping two repos alive doubles your bugs and decisions. The fastest path is to pick one repo as the source of truth, then treat the other as a feature donor only.
Choose the base that is safest and easiest to ship, even if the UI looks less polished. Safety means fewer unknowns, fewer shortcuts, and fewer places where one change breaks three screens.
If you’re stuck, evaluate both repos on a few real-world checks:
- Can someone new run it locally without detective work?
- Does auth actually work end-to-end (signup, login, reset, logout)?
- Are secrets handled safely (not hard-coded or exposed)?
- Is the data model consistent (one clear schema, minimal hacks)?
- Can you deploy it without one-off manual fixes?
Once you pick the winner, freeze the other repo. No new features, no “quick fixes,” no parallel rebuild. Keep it read-only so it can’t quietly drift and pull the team back into split-brain development.
Next, write a short must-keep list from the losing repo. Describe outcomes, not screens: “users can export invoices,” “admins can refund,” “customers can update payment method.” That becomes your migration backlog.
Finally, document your non-negotiables in one place: users, payments, permissions, and the core flows that keep the business alive. Examples:
- Existing users must log in with the same email.
- No double-charging.
- Only admins can view customer data.
Step-by-step: migrate features without copying the bugs
The safest approach is boring: move one working user flow at a time and prove it works before touching the next one.
Start with the smallest vertical slice you can ship end-to-end. Pick a flow that touches UI, backend, and data, but stays contained (for example: sign up, create one item, see it on a list). This quickly reveals routing, API shape, and database assumptions without dragging you into endless edge cases.
Port behavior, not code
Treat the old repo as a spec, not a source file to copy. Read what it does, then re-implement that behavior cleanly in the new repo. Copying files is how you import hidden globals, insecure queries, and "works on my machine" hacks.
A practical loop:
- Write down the expected inputs, outputs, and failure messages for the flow.
- Rebuild the endpoints and UI based on that behavior.
- Keep data model changes minimal until the flow is stable.
- Add a small feature flag (even a config toggle) so you can turn the new flow on and off.
Once the slice works, move the next feature the same way. Keep migrations small and keep pull requests focused. Migrating two unrelated features at once makes it hard to tell what broke.
Verify after each move
After each feature, run the same quick checks:
- Complete the flow twice (new user and existing user).
- Verify the data written to the database matches what you expect.
- Confirm no new errors or warnings appeared in server logs.
- Confirm you can roll back (flip the toggle back).
If one codebase has teammate invites, don’t copy the invite code verbatim. Recreate the invite behavior (who can invite, what gets sent, how acceptance works), then confirm it doesn’t leak tokens in logs.
High-risk areas: auth and data migrations
When you merge two codebases, the parts most likely to break in production are authentication and data. They often look “done” in a demo, but small differences between repos can lock users out, leak data, or corrupt records.
Authentication: prove it end-to-end
Audit auth before moving nice-to-have features. Don’t just check that a login page exists. Check the full loop: sign-in, session storage, logout, and how errors behave.
Your basic auth checks should cover:
- Login works with real accounts, not only demo users.
- Sessions persist across refresh and expire when they should.
- Password reset tokens work and can’t be reused.
- OAuth callbacks match the right domains and redirect paths.
- Roles and permissions match what you actually intend (admin vs member vs guest).
One common failure during migration: Repo A uses cookie sessions while Repo B uses local storage tokens. Both can “work” alone, but mixing them creates random logouts and broken protections.
Data migrations: map the model, then move it safely
Before you migrate features, write down the data model in plain English: tables or collections, required fields, relationships, and what can be null. If the same concept is named differently (userId vs owner_id), treat it as a migration problem, not a search-and-replace task.
Plan migrations like a controlled release:
- Take a backup you can restore quickly.
- Rehearse on staging with realistic data volume.
- Define rollback (and what it means if partial data already moved).
- Migrate in small batches when possible.
- Validate totals and spot-check critical records (users, payments, permissions).
Verification on a tight timeline: tests you actually need
Speed matters, but skipping basic checks is how you ship the same bug twice. The goal isn’t perfect coverage. It’s confidence that the new source of truth works for real users.
Start by locking a minimum set of end-to-end checks. These are the flows that prove the app is usable and money-safe:
- Sign up and onboarding (whatever your real process is)
- Log in, log out, and password reset
- The core workflow users actually pay for
- Payments and refunds (if you have them), including a failed payment
- One admin or settings action that changes data
Then add a few cheap automated checks that catch breakage early:
- Linting and formatting
- Type checks (if you use TypeScript)
- A small number of unit tests where the logic is stable
Keep staging close to production. Use the same environment variable names and loading method, and match the database type. A classic failure is “works on staging” because staging uses SQLite while production uses Postgres.
As you verify, keep a short bug diary: what broke, where it was fixed, and what would have caught it earlier (a test, a linter rule, a missing env var). This prevents the same bug returning during later migrations.
Common traps that recreate the same mess
Most teams get into trouble when they treat merging as a simple “best of both” exercise. If both repos were produced quickly by different AI tools, they often share the same weak spots, just in different places.
These traps tend to recreate the mess:
- Doing one giant merge, then spending weeks untangling conflicts and duplicate logic.
- Copy-pasting whole files to move features and importing insecure patterns (hard-coded secrets, unsafe SQL, missing auth checks).
- Changing UI and backend at the same time, so you can’t tell which change caused the break.
- Letting dependencies drift, then builds fail on a clean machine or in CI.
- Treating deployment as a final step, then discovering late that env vars, migrations, or hosting assumptions don’t match reality.
A small example: you copy a “working” login page from Repo B into Repo A. It looks fine, but it also brings a helper that logs tokens to the console and skips server-side session checks. You fixed the screen, but you reintroduced the security hole.
Guardrails that keep you moving:
- Move one feature slice at a time and add a checkpoint before the next.
- Re-implement minimal behavior in the winning repo instead of copying files.
- Pin runtime and package versions early, then verify clean installs.
- Do a “deploy early” dry run as soon as the first migrated feature lands.
Quick checklist before you commit to the switch
Before you merge two codebases into one path, pause and make sure you can live with the decision for the next few weeks. The goal is predictable shipping and fewer surprises.
First, make the losing repo safe to keep around without letting it keep changing. If people can still push quick fixes there, you’ll end up with two versions of reality again.
Use this as a gate:
- The old repo is frozen (read-only), clearly marked as archived, and you recorded the last known good commit or tag.
- The chosen repo builds from scratch on a clean machine using written steps (install, env vars, build, run), and those steps work twice in a row.
- Deployment is repeatable, and you can roll back to the previous build.
- Login and signup work end-to-end for new and existing users, including password resets and session expiry.
- No secrets are committed, and environment variables are documented.
A concrete way to validate the last item: run the top three user journeys on staging (for example: sign up, complete the main task, pay or export), using test accounts and production-like data volume.
Example: choosing between a v0 build and a Replit rebuild
A founder ends up with two versions of the same app. The first is a v0 build that looks great and has most screens, but it’s mostly frontend. The second is a Replit full-stack rebuild that can log in and save data, but the UI is rough and parts of the logic are duplicated.
The goal isn’t to merge line-by-line. It’s to pick one repo as the source of truth, then move only the parts that earn their keep.
They compare both repos using a few checks:
- Which one has working authentication end-to-end (signup, login, logout, session expiry)?
- Which one has a cleaner data model (clearer names, fewer one-off fields)?
- Which one deploys without manual steps or secret keys scattered in the repo?
- Which one has fewer “magic” fixes (hard-coded IDs, hidden admin routes, random timeouts)?
In this case, the Replit repo wins because auth works and the data model is closer to what the business needs. The v0 repo becomes a design reference only.
Migration happens feature by feature. Instead of copying the entire v0 UI, the team rebuilds the key screens as components inside the Replit repo, wired to the existing backend. They start with the highest value flows: onboarding, the main dashboard, and the one action users do every day.
Before calling it done, they validate behavior, not just visuals. Roles and permissions need to match, forms need the same required fields, and error states must be clear (wrong password, missing field, failed save).
Next steps: get to one shippable codebase
If you need to merge two codebases, the fastest way to stop the chaos is to pause feature work and do a short written audit. You’re not judging code style. You’re identifying what’s safe to ship and what will break later.
Write down what you know today:
- The most painful user-facing bugs (what, where, how to reproduce)
- The biggest risks (security, data loss, surprise costs)
- The features you must keep (and what can wait)
- What’s already working in production (even if it’s ugly)
- What blocks deployment (env vars, build steps, missing migrations)
Then make one decision: fix and migrate, or rebuild from scratch using the same requirements. If one repo has a stable data model and predictable deploys, it often wins even if the UI is behind. If both repos are shaky, a clean rebuild can be cheaper than dragging forward two sets of problems.
Bring in help as soon as you see red flags like exposed secrets, broken auth, unclear database ownership, or deploys that only work on one machine.
If you inherited AI-generated prototypes and want one production-ready codebase, FixMyMess (fixmymess.ai) is built for this exact situation. They can diagnose both repos, repair broken logic, harden security, refactor messy architecture, and prep the app for deployment. If you’re not sure which repo should win, starting with their free code audit can give you a clear, low-drama plan before you commit.
FAQ
Should I merge the two repos or pick one and migrate?
Most teams should pick one repo as the source of truth and migrate features intentionally. Keeping both “alive” usually doubles bugs, security holes, and decision-making, and it gets worse every week.
How do I choose the winning codebase if I’m not technical?
Pick the repo that is safest and easiest to ship, not the one that looks nicest. Favor the one that runs from a clean install, deploys repeatably, has working auth end-to-end, and has fewer hacks like hard-coded URLs or hidden bypasses.
What does it mean to “freeze” the losing repo?
Make it read-only and set a clear rule that all new work happens only in the chosen repo. Keep the losing repo for reference and comparison, but stop shipping from it so it can’t quietly drift back into a second product.
What’s a quick way to compare two AI-generated codebases?
Start with the same basic checks on both: clean install, run locally, build, deploy, and predictable errors. Then look for obvious red flags like committed secrets, auth bypasses, unsafe database writes, or API routes with no access checks.
Why is a line-by-line merge usually a bad idea?
Because they often disagree on core assumptions like data models, auth sessions, and business rules. You usually end up with a third codebase that inherits the worst parts of both and is harder to debug than either original.
How do I migrate features without copying bugs?
Port the behavior, not the files. Treat the losing repo like a spec: write down inputs, outputs, and error states, then re-implement that behavior cleanly in the source-of-truth repo so you don’t import hidden globals, insecure queries, or “works on my machine” shortcuts.
What’s the fastest safe migration plan on a tight timeline?
Start with a small vertical slice that touches UI, backend, and data, such as sign up and creating one record. After each move, run the flow twice, check what was written to the database, and confirm logs don’t show new errors so you catch drift early.
What are the highest-risk parts when combining two versions of the same app?
Authentication and data migrations. If you get sessions, roles, resets, or permissions wrong, users get locked out or see the wrong data, and if you migrate the model carelessly you can corrupt records or break reporting.
What minimum testing do I need before switching to one repo?
Run a small set of end-to-end checks for the flows that keep the business alive, especially login/logout/reset and the core workflow users pay for. Add lightweight automation like linting and type checks so obvious breakage doesn’t slip in during migrations.
When should I bring in outside help, and what can FixMyMess do?
Bring in help when you see exposed secrets, broken or inconsistent auth, unclear database ownership, or deploys that only work on one machine. FixMyMess specializes in diagnosing AI-built codebases, choosing a safe source of truth, and getting you to a production-ready app quickly, often starting with a free code audit to map risks before you commit.