Secure AI-generated admin panel: routes, logs, and safety
Secure AI-generated admin panel with locked routes, audit logs, safe deletes, and guardrails so one bug cannot wipe your data.
What usually breaks in an AI-generated admin panel
AI-built admin panels often look finished, but they tend to be "works on my machine" secure. The UI hides buttons, the happy path works, and nobody tests what happens when a curious user pokes the API directly.
The most common gap is confusing the screen with the system. A page might be labeled "Admin", but the server still answers the same requests for anyone who can guess a URL, reuse an old token, or run a simple curl command.
Here are the failure modes we see again and again in a secure AI-generated admin panel review:
- Admin pages that load without a real server-side role check
- APIs that trust client input (like userId, orgId, or role)
- No audit trail, so you cannot tell who did what after an incident
- Destructive actions that run instantly (delete, purge, bulk updates)
- Overpowered admin accounts used for routine tasks
The "one bug deletes everything" risk usually comes from two things stacked together: a broad query (like "delete all users where status = inactive") and a missing scope check (like tenant or environment). A tiny bug in a filter, a missing WHERE clause, or a mistaken default can turn a normal cleanup into a full wipe.
Picture a founder using a bulk action to remove test accounts. The UI says "10 selected", but the server ignores the selection array and runs the operation on all rows that match a loose condition. With no confirmation step and no audit log, the first sign is customers emailing that their data is gone.
This post focuses on practical hardening: locking down routes on the server, adding logs that answer real questions, and putting safety rails around destructive actions. If you inherited an AI-generated panel from tools like Lovable, Bolt, v0, Cursor, or Replit, FixMyMess can quickly audit the risky spots before they bite you.
Define roles and the few actions that truly need admin access
A secure AI-generated admin panel starts with a simple idea: most people should be able to see more than they can change. If you skip this step, you end up with a single “admin” switch that quietly grants the power to break production.
Write down the real jobs your admin area supports. Keep it short and specific, like “reset a user’s password,” “pause a subscription,” or “edit homepage copy.” If you cannot name the job, it probably should not exist as a button.
Pick roles that match real people
Avoid fancy role systems. Four roles cover most teams:
- Owner: full access, including billing and role changes
- Admin: day-to-day changes, but no owner-only controls
- Support: user help actions with limited write access
- Read-only: can view everything, cannot change anything
Then split permissions into “view” and “change.” A support person might need to view invoices to answer questions, but should not be able to issue refunds.
Identify the “most dangerous” actions first
Mark the actions that can cause irreversible damage or money loss. These usually include:
- Delete data (users, orgs, projects, tables)
- Change roles or ownership
- Refunds, credits, or plan changes
- Rotate API keys or change auth settings
- Bulk actions (bulk delete, bulk disable)
A quick example: if Support can “disable a user,” that might be fine. But if the same screen also allows “delete user,” the difference matters. Disable is reversible. Delete is not. Treat them as different permissions, even if they sit next to each other in the UI.
If you inherited an AI-built admin panel and everything is lumped under one admin role, that is a common FixMyMess audit finding. The fastest win is to reduce who can do the top 3 destructive actions before touching anything else.
Lock down admin routes the safe way (server-side, not UI-only)
An admin panel often looks protected because the UI hides buttons. That is not protection. If someone can guess a URL, reuse an old session, or call an API directly, they can still hit admin endpoints. A secure AI-generated admin panel starts with one rule: every admin page and every admin API must enforce access on the server.
Confirm that every admin screen requires login, not just the dashboard. Common misses are “secondary” pages like user management, billing, feature flags, exports, background jobs, and internal tools. If one page loads without a server check, it can become the entry point.
Put the check where it cannot be skipped
Do the authorization check in a single place that runs on every request to admin routes (middleware, route guard, controller wrapper, whatever your stack calls it). Do not rely on client-side state like “isAdmin” stored in local storage.
Use an explicit allowlist for admin routes and admin APIs. This is simple and safe: you declare what is admin, and everything else is treated as non-admin.
- Allowlist admin paths (for example,
/admin/*) and admin API prefixes (for example,/api/admin/*). - Require a valid session, then check the role on the server.
- Deny access if the role is missing, stale, or unverified (no “fallback to user”).
- Re-check on sensitive actions, not only on page load.
- Log and return a clear “forbidden” response, not a redirect loop.
Deny by default for anything new
AI-generated code often adds new routes quickly and forgets to secure them. Add a simple rule: any new route under admin or any new admin API must be blocked unless it is registered in the allowlist and covered by the server-side guard.
If you inherited an AI-built project from tools like Bolt or Lovable, FixMyMess often finds “hidden” admin endpoints that never got a real server check. Catching those early is usually the fastest risk reduction you can make.
Harden the admin APIs behind the UI
An admin panel is only as safe as the APIs it calls. A button hidden in the UI does not matter if the endpoint still works for a normal user, a leaked session, or an anonymous request.
Start by treating every admin endpoint as a locked door. Require server-side auth, then check role or permission on every request. Do not rely on a single “isAdmin” flag from the browser. Re-check on the server using trusted session data.
Next, be strict with inputs. Admin endpoints often accept IDs, search terms, date ranges, or filter objects. Validate type, length, and allowed fields, and reject anything unexpected. If an endpoint accepts raw SQL fragments, unbounded regex, or “sort by any column”, it will eventually hurt you.
Here are a few guardrails that make a secure AI-generated admin panel much harder to break:
- Require explicit IDs for writes (update, disable, delete). Avoid “apply to all matching filter” writes.
- Add pagination on reads and hard caps on bulk operations (for example, max 100 items per request).
- Force a “preview step” for bulk actions: return the count and sample records before allowing the write.
- Rate-limit sensitive endpoints like password resets, role changes, and exports.
Bulk actions are the usual disaster path. A common bug is a missing tenant filter or a null parameter that turns “delete these 3 users” into “delete all users”. If you must support bulk updates, make the request include both a filter and an explicit limit, and fail if the result set is larger than expected.
Finally, return clear errors without leaking internals. Say “Not authorized” or “Invalid input: userId must be a UUID”, but do not echo stack traces, secrets, SQL, or file paths. If you inherited a shaky codebase, FixMyMess often starts by auditing these admin endpoints first, because one unsafe API can undo every UI fix.
Prevent destructive actions from turning into disasters
Admin panels often have the sharpest buttons in the product: delete users, reset billing, purge data, bulk update. In a secure AI-generated admin panel, the goal is simple: make it hard to do irreversible harm by accident, and easy to recover when something still goes wrong.
Start by separating “remove from view” from “erase forever”. For user-facing or critical records, prefer soft delete (mark as deleted) with a clear restore path. Keep hard delete rare and tightly controlled. Even better, make hard delete an offline, time-boxed operation, not a normal button next to “Edit”.
For irreversible actions, a modal is not enough. Use a typed confirmation that forces attention, like requiring the admin to type the exact resource name or a phrase such as DELETE PROJECT. This blocks misclicks, and it also protects you from UI glitches that double-submit.
High-risk actions should have a second check that lives on the server, not just in the browser:
- Re-authentication before deletion (password or SSO step-up)
- A one-time code sent to a trusted channel
- A second-person approval for org-wide actions
- A short delay window where the action can be canceled
Under the hood, wrap destructive changes in a database transaction so you do not end up with partial deletes (some tables updated, others not). If the operation touches files, queues, or external services, record a single “operation ID” and make the job idempotent so retries do not multiply the damage.
Finally, add rate limits and cooldowns. For example: allow one “bulk disable” per minute per admin, and cap batch sizes. This turns a runaway script or a buggy bulk action into a small incident instead of a total wipe.
If you inherited an AI-built panel where these safeguards are missing, FixMyMess can quickly audit the risky paths and add the guardrails before you ship.
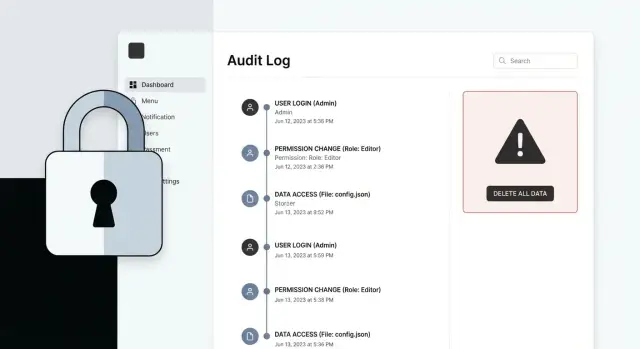
Add audit logs that answer real questions during an incident
When something goes wrong in a secure AI-generated admin panel, the first question is not “what happened?” It’s “who did it, from where, and what exactly changed?” Good audit logs let you answer that in minutes, not hours.
Log the facts you will actually need
Capture enough detail to replay the story without guessing. For every admin action (create, update, delete, bulk actions, permission changes), record:
- Who: user ID, email, role at the time of the action
- What: action type (for example, UPDATE_USER_ROLE), and the UI or API route
- When: timestamp in a single standard timezone (often UTC)
- Where: IP address and a simple user agent or device fingerprint
- Target: the record(s) touched (table/entity + ID), including counts for bulk actions
For high-risk fields like role, status, permissions, payout settings, or feature flags, include before and after values. You do not need to store every field on every update, but you do want enough to prove what changed.
Add a request ID to each log entry and include it in server responses. When a report comes in (“all users got downgraded”), you can search by request ID and follow that single chain across services.
Make logs searchable and protected
Logs are only useful if you can filter them fast: by user, action type, target ID, and time range. During an incident you will also want “show me everything this user did in the last hour” and “show me all DELETE actions today.”
Decide retention up front (for example 30-180 days depending on risk) and restrict who can view logs. Audit logs can contain sensitive data, so treat them like production data: access control, tamper resistance, and careful redaction of secrets.
If you inherited an AI-built admin panel with missing or noisy logs, FixMyMess typically starts by mapping the real admin actions and adding consistent audit events, then verifying them with a short incident-style walkthrough.
Realistic example: the bulk action that wipes more than intended
A common failure in a secure AI-generated admin panel is the “bulk action” that assumes the UI will keep things safe. Here’s a real scenario: a support admin wants to deactivate one user who is spamming tickets. They filter by email domain to find the account, but the filter is loose (for example, @gmail.com) and matches thousands.
The UI shows one selected row, but the backend endpoint accepts “apply to all matches.” Because role checks are missing or too broad (any logged-in staff can call it), a single click triggers a mass update: thousands of users are deactivated, sessions are invalidated, and support volume spikes.
Guardrails that prevent this kind of accident are simple and boring, which is exactly what you want:
- Put role checks on the server for every admin action, not just on the page.
- Cap bulk actions (for example, max 25 records) and require a narrow, explicit selection.
- Show a preview: “You are about to change 3,214 users” before anything happens.
- Require a typed confirmation for destructive actions (type the exact word or the count).
- Wrap the change in a transaction so partial updates do not leave data in a broken state.
When something still goes wrong, audit logs turn panic into a plan. A useful log entry answers: who did it, from where, which endpoint, which filter or IDs were used, how many records changed, and a short before/after summary of key fields.
Recovery should be designed, not improvised. If “deactivate” is a soft action, you can restore by flipping a flag back using the same IDs from the audit log. For deletions, prefer soft delete with an easy restore window. If you must hard delete, you need a tested rollback path (backups plus a rehearseable restore procedure). Teams often ask FixMyMess to add these guardrails after an AI-built admin panel shows this exact failure mode in production.
Reduce the blast radius: secrets, sessions, and least privilege
A secure AI-generated admin panel is not just about blocking the wrong people. It is about making sure a single mistake does not expose everything.
Start with secrets. AI-built panels often hardcode API keys, database URLs, or admin “setup” tokens in config files, seed scripts, or even visible admin screens. Move all secrets to environment variables, rotate anything that may have leaked, and remove any “show config” widgets or debug endpoints that print sensitive values.
Sessions and tokens deserve tight limits. If an admin token lives for weeks, it becomes a long-term skeleton key.
Make access easy to revoke
Keep admin access short-lived, scoped, and easy to kill. A simple policy that works for most teams:
- Short session lifetime for admins (hours, not days)
- Re-auth for risky actions (exports, role changes, deletions)
- Per-user sessions so you can revoke one person without logging out everyone
- Token scope limited to the admin app, not your whole platform
Next, limit what the admin app can do at the database level. Many AI prototypes connect as a superuser because it “just works.” Give the admin app a dedicated database user with only the permissions it needs. If the admin UI never needs to drop tables, it should not be able to.
File uploads and exports can quietly become data leaks. Treat uploads as untrusted, validate type and size, and store them outside your app server with private access. For exports, avoid putting raw files in a public folder, and add an expiry time so old exports do not linger.
Finally, add basic defenses that reduce accidental exposure: security headers to limit risky browser behavior, and CSRF protection if your admin uses cookies for auth. If you are not sure where the weak spots are, FixMyMess can run a free code audit and point out the places where one bug could turn into a full breach.
Common mistakes that keep admin panels fragile
The most common reason an admin panel fails a security check is simple: the UI hides buttons, but the server still trusts the browser. If someone can call the API directly (or your own front end makes a mistake), client-side role checks do nothing. A secure AI-generated admin panel needs server-side rules that are enforced on every request, even if the UI looks perfect.
Another fragile pattern is a single isAdmin flag that means “all power, everywhere.” It usually grows over time until one account can edit users, view billing, change permissions, and run bulk deletes. When something goes wrong, there is no easy way to answer: who did what, and why did they have access?
Destructive endpoints are often the scariest. AI-generated code may include “delete all,” “reset,” or bulk actions with no caps and no preview. One typo in a filter or one bug in a loop can delete far more than intended. If the endpoint is not idempotent (safe to retry) and has no safeguards, you can also get double-deletes during retries or timeouts.
Audit logs are another trap. Teams either log too little (no target record, no before/after, no actor), or they log too much (tokens, passwords, full request bodies, personal data). The goal is to record useful facts without turning logs into a second data leak.
Watch for these red flags in production builds:
- Role checks only in the front end, not on the API
- Debug routes, test admin accounts, or “temporary” bypass flags left enabled
- Bulk actions with no preview, no limit, and no confirmation step
- No request IDs or action IDs, making incidents hard to trace
- Logs that include secrets, session tokens, or raw password fields
A small example: a “Deactivate users” bulk action takes a list of IDs, but a bug sends an empty list. The server interprets empty as “all users” and deactivates everyone. A simple guard (reject empty, cap the max, require a preview count) prevents the disaster.
If you inherited an AI-built admin panel and you are unsure where these risks are hiding, FixMyMess can run a free code audit to flag the fragile parts before they bite you in production.
Quick hardening checklist before you ship
Run this checklist when you think your admin panel is “done”. It catches the failures that show up only after real users and real data.
Five tests to run in 15 minutes
- Anonymous access test: copy an admin-only URL, open it in a private window, and try it without logging in. It should fail every time, even if the UI hides the button.
- Server-side permission test: pick one admin action (like “create user” or “refund”), then call it with a normal account. The API must reject it, not just the page.
- Audit trail test: do three actions (view, edit, delete) and confirm each creates an audit record with who did it, what changed, when, and the target ID. If you can’t answer “who deleted this?” in one minute, logging is not done.
- Bulk action safety test: try a bulk operation using an overly broad filter (for example, “all users created this month”). You should hit a hard cap and an extra confirmation step that spells out the exact count and impact.
- Recovery test and key hygiene: soft delete something, then restore it end-to-end (UI, API, database). While you’re there, rotate any secrets that have ever been printed to logs, shown in the UI, or committed to a repo.
A quick reality check: if one bug can turn a “Delete one” into “Delete all”, you don’t yet have a secure AI-generated admin panel. Add caps, confirmations, and safe defaults before shipping.
If you inherited an AI-built admin panel and you’re not sure what to test, FixMyMess can run a free code audit to find the risky parts fast.
Next steps: get a quick audit and fix the risky parts first
If you want a secure AI-generated admin panel, start by choosing what you can harden today and what deserves a deeper refactor. Small changes can remove the biggest risks fast, even if the codebase is messy.
A good “today” plan is anything that blocks easy disasters: server-side route checks, safer destructive actions, and audit logs that let you answer who did what. A “refactor later” plan is usually architecture work: untangling permissions, cleaning data access patterns, and removing copy-pasted logic that makes bugs hard to spot.
If your admin panel was generated by Lovable, Bolt, v0, Cursor, or Replit, assume there are hidden edge cases. The UI can look fine while the API still accepts direct requests, bulk actions run without limits, or an “admin only” page loads with a normal user session.
A fast way to de-risk in 48-72 hours
A focused codebase diagnosis should cover the parts that cause real damage:
- Auth and session handling (how “admin” is decided)
- Admin routes and API protection (server-side only)
- Destructive actions (delete, bulk edit, imports) and safety rails
- Audit logging (what gets recorded, and what’s missing)
FixMyMess can run a free code audit and call out the high-risk issues first, then help turn a fragile prototype into production-ready software with human-verified fixes.
What to prepare before you hand it off
You will get better results if you collect a few items up front:
- Repo access (or an exported codebase)
- A simple list of admin roles (even if it’s “owner” and “staff”)
- The scariest actions in your panel (bulk delete, refunds, user bans, data exports)
- One real incident you worry about (“one bug deletes everything”)
With that, you can fix the riskiest parts first, ship with confidence, and schedule deeper cleanup when you have breathing room.